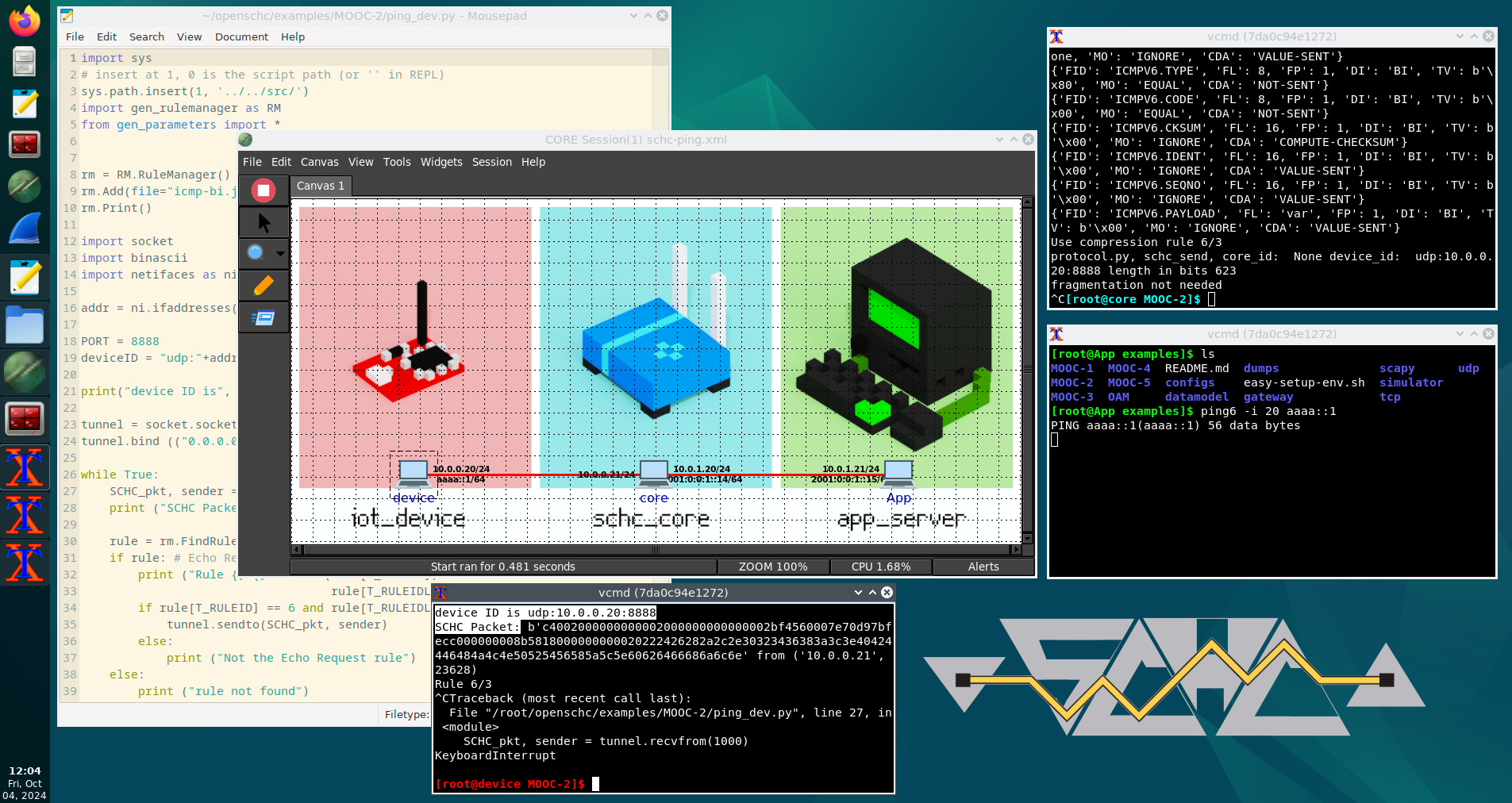
OpenSCHC VM
Welcome to the OpenSCHC Virtual Machine website! Here, you can download a VM based on Debian 12 (x64) containing the CORE network simulator with the SCHC deployment scenario. This environment enables hands-on exercises, complementing The book of SCHC for effective learning.